We’ve gathered some useful info about the market’s perspectives, communication standards, mobile app development (including cross-platform mobile app development) options, security side and core features of an app that your users would love.
State of the smart home market
The smart home is a setup of in-home internet-connected devices that are remotely controlled via a smartphone or other networked device. Being a part of the Internet of Things (IoT), smart home devices typically function together and share usage data among themselves to adjust automatically to the family members’ preferences.
Smart homes came to life in 1975 with the release of Pico Electronics’ X10. A wired protocol for home automation, X10 allowed managing household appliances through power lines.
In 1984 National Association of Home Builders launched a Smart Home Special Interest Group. Its task was to advocate the technology for home-building methods.
The future of the smart home looks inviting with the revenue estimated at US$48,730m in 2018. The revenue is projected to grow at an annual rate of 25.0%, resulting in a market volume of US$119,088m in 2022.
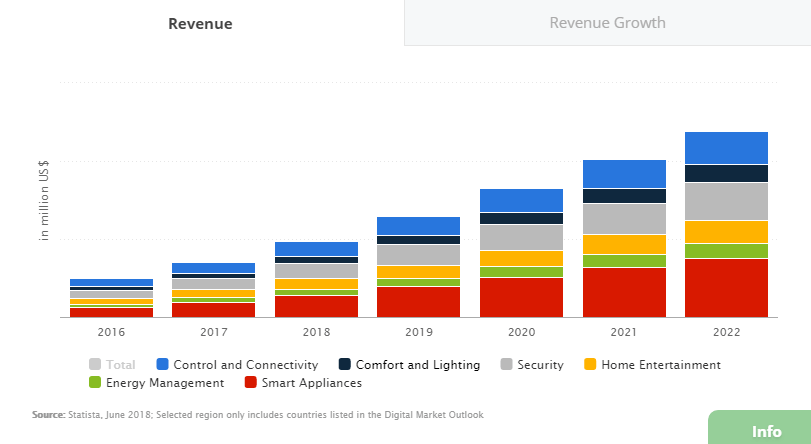
The household penetration rate is currently (as of June 2018) at 7.5% and is supposed to reach 19.5% by 2022. In the meantime, the Control and Connectivity segment will see 216.9 active households by 2022.
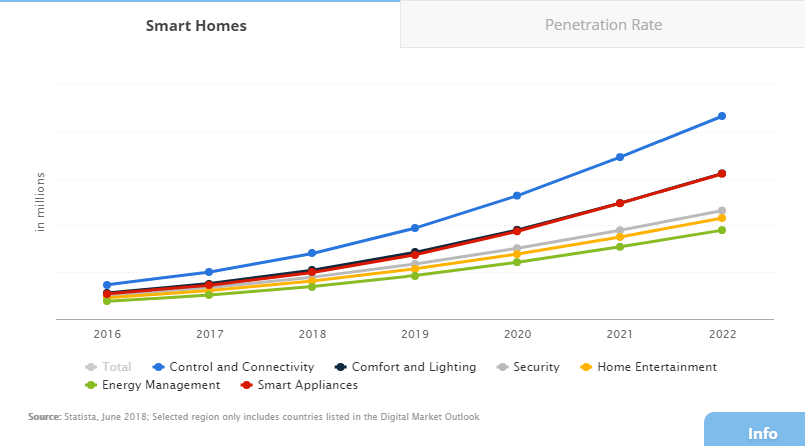
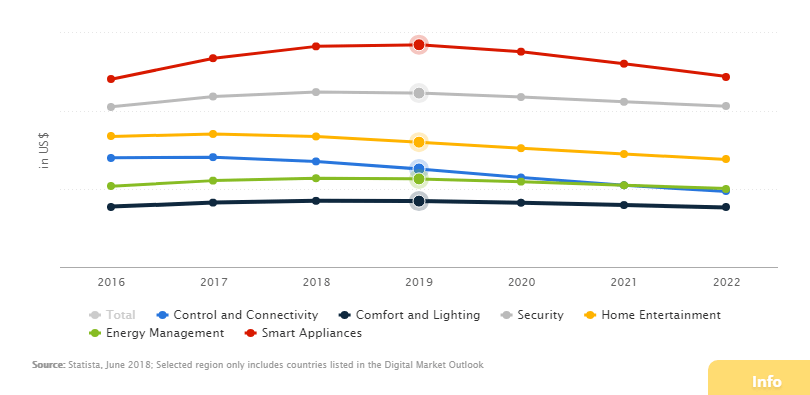
The average revenue per installed smart home currently amounts to US$135.36.
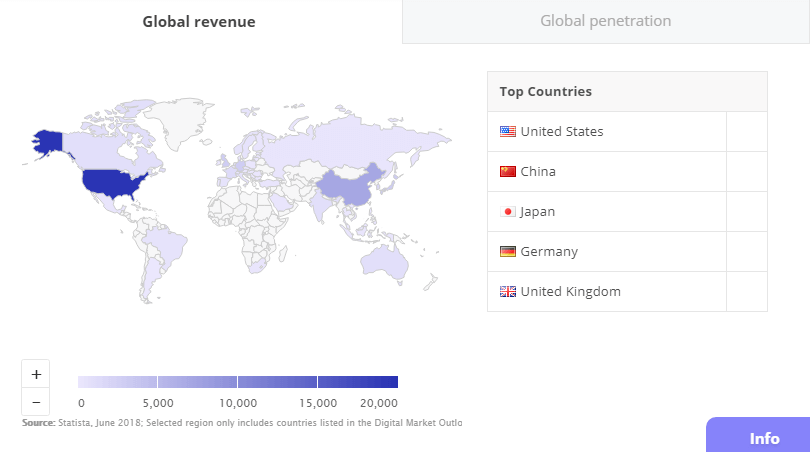
With the revenue of US$19.827m as of 2018, the United States is leading the smart home market economy.
According to Smart home market report, the market key growth-driving factors are:
- increasing awareness related to safety and security;
- increasing consumer need for simplicity and personalized experience;
- the growing adoption of cloud-based technologies.
How a does smart home talk?
Smart devices are electronic gadgets that leverage protocols to communicate. A protocol means the style in which a signal is transmitted from one device to another to launch an action. Put it differently, it is a language for the devices to talk to each other.
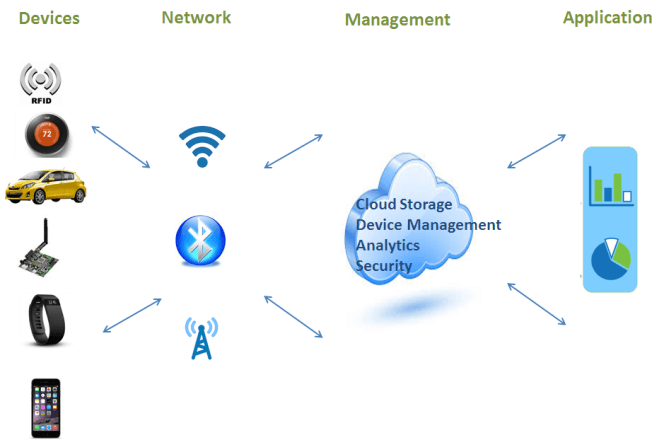 Source: dellemc.com
Source: dellemc.com
Devices that use the same protocol can communicate and can be managed via a single mobile app. The gadgets with different protocols can’t interact (in the majority of cases) and should be controlled via separate apps.
At least, unless dedicated tools like multiple protocol smart hubs enter the scene. Smart home hubs are central units that allow to control all IoT devices in the house and relay commands to them via a mobile app. One has a wide variety to choose from.
But until you get a solution like SmartThings or Harmony, it is worth knowing why smart home manufacturers use the protocols they do.
Basically, there are two types to choose from: wired and wireless.
X10 is a pioneer of the connected abode, that is currently both wireless and wired. The protocol was designed to utilize your home’s existing powerline, so no additional cables needed. Currently, X10 is also able to send wireless signals. The image from X10 casts light on the way the thing works.
 Source: x10.com
Source: x10.com
X10-powered devices have an appealing price tag and boast a wide variety of solutions available on the market. However, given its age, the protocol has a number of flaws:
- only 256 devices can be addressed in a single network;
- lack of encryption;
- subject to interference;
- limited functionality (defines only 16 commands);
- slower than modern alternatives;
- commands can get lost.
Insteon is a dual-mesh home automation protocol launched by SmartLabs in 2005. It was designed to bridge the gap between powerline and wireless radio frequency communication and uses both. Insteon devices repeat messages over both channels, ensuring a fail-safe backup path. Insteon claims, that the technology makes errors 100 times less likely.
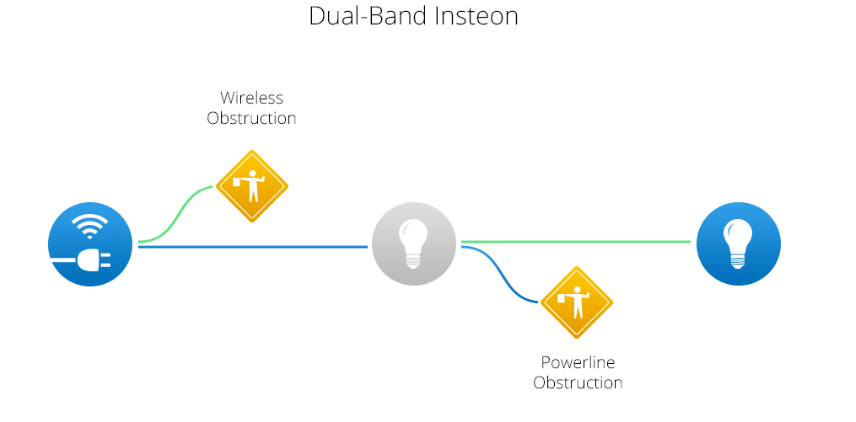 Source: insteon.com
Source: insteon.com
All Insteon devices can act as repeaters that receive and retransmit every command they get across the network. It makes the system interlocked and strong, unlike routed networks, where the connection can be lost when a single device fails. The communication range is 150ft (45m) unobstructed line-of-sight.
Each Insteon device has its unique ID, that makes them secure from external control or eavesdropping (which may be the case with X10 and UPB). Security is further advanced with messaging encryption.
Insteon enables to reach more than 16 million addresses and execute 65000 basic commands. Today it is supported by a wide range of products, as you can see in the company's catalog.
Z-Wave is a purely wireless home automation protocol. It was developed by Zensys, introduced in 2001 and currently owned by Silicon Labs. It was specifically designed for the low power, low bandwidth needs of the smart home, which makes Z-Wave battery-efficient.
Z-Wave operates on the 800-900 Mhz radio frequency range. The reason you might care about this is that it does not use 2.4GHz (Wi-Fi, Bluetooth, and ZigBee frequency), and is not subject to the interference. However, Z-wave devices’ frequency depends on the location, which may cause inconveniences when moving places.
Z-Wave is a mesh network, where devices route the message to each other until it reaches the destination point. The protocol allows covering the physical range of 328 ft (100m) in the open air, which makes it beautiful for larger houses. The technology supports up to 232 devices in one smart home network, which still more than suffices for most households. Unique IDs and AES-128 symmetric encryption are inborn.
The asset of Z-Wave is its superb interoperability with backward compatibility to all versions. Z-Wave is supported by its alliance, a global consortium of more than 700 companies creating products and services powered by Z-Wave. You can find an impressive list of the members here. Today, there are over 2400 certified interoperable Z-Wave products worldwide.
Zigbee originated in 1998, was standardized in 2003, and revised in 2006. It shares a plethora of features with Z-Wave. A wireless mesh network, Zigbee is meant for embedded applications that require low power consumption and tolerate low data rates. It ensures a long life for battery-operated devices.
Still, Zigbee is faster (40-250 kbps vs. 9.6-100 kbps) and therefore requires more energy to cover the same range as Z-Wave. Transmission range varies from 32-328ft (10-100m), depending on power output and environmental characteristics.
Zigbee uses 2.4 GHz as its global standard frequency. However, with many protocols residing there, local interference can occur.
The technology is equipped with the same encryption type as Z-Wave, but there were some reports of its vulnerability.
Zigbee can support 65.000 nodes on the mesh network, and around 2500 products from 400 members of its alliance are certified.
However, as an open standard, Zigbee somewhat lacks control over the interoperability. So the devices running it do not necessarily work in concert with each other. Despite many similarities, Zigbee is also not directly compatible with Z-wave.
Introduced in 2015, Thread is an open wireless protocol that was designed in the search for a “golden standard” for the Internet of Things. Today, its alliance is supported by big players like Nest Labs (acquired by Google), Samsung, ARM, Freescale, and more. Thread operates on 2.4 GHz with AES-128 encryption and is designed to support low-power smart home products. The protocol forms a “self-healing” mesh network, that allows to link around 250 devices at the range of 100 ft (30m). And it is enough for most households. Thread devices are IP-based and do not rely on home internet connection or Wi-Fi.
One issue with all protocols mentioned above is that they can’t directly connect to smartphones, tablets, or laptops. So, first, they need to talk to a hub, that can also be specifically designed for one protocol or one manufacturer’s products. The hub will further connect to your home network either via a Wifi or Internet router.
But there are the alternatives.
Bluetooth is not just for listening to music and working with your mobile hands-free. Its edition, Bluetooth Low Energy (BLE) is also a keystone of connected homes, lying in the heart of a variety of smart devices.
Also dubbed Bluetooth Smart, BLE was introduced as part of the Bluetooth 4.0 specification by Bluetooth Special Interest Group in 2010. It is integrated into Android, iOS and Windows operating systems and BLE devices can be accessed directly from one’s smartphone or tablet.
Compared to Classic Bluetooth, Bluetooth LE is designed to reduce power consumption and cost, while maintaining nearly the same communication range (roughly 330ft/100m). BLE, however, is not suitable for data-heavy applications. It BLE also uses 2.4 GHz radio frequencies and runs the risk of interferences. In July 2017, Bluetooth mesh networking capability was added with about 32.000 nodes support, which allows creating a large-scale and reliable system.
BLE mesh has robust security (AES-CCM and 128-bit keys applied) and should spend as little energy as BLE processors did before. According to ABI Research, 650 million Bluetooth smart home devices will ship in 2018.
Wi-fi was never meant for home automation and can’t compare with other protocols in power efficiency for low-bandwidth communications. Yet, it is extremely popular among smart home protocols due to its ubiquitous presence.
Wi-Fi operates on either a 2.4 GHz or a 5 GHz frequency. It uses a router to create a local network of your smart home gadgets, with devices freely interacting. Wi-Fi range depends on a number of factors, but a general rule is that traditional 2.4 GHz band ensures the reach of up to 150 ft (46m) indoors and 300 feet (92m) outdoors.
As usual, the speed depends on the router and one's internet provider. The main downside of Wifi scenario is its relatively high power consumption so your devices will need strong batteries. It makes the protocol suited for a smaller number of devices, where bandwidth is of higher importance, such as smart security cameras. For a light bulb, for example, Wifi won’t make much sense.
Theoretically, you can connect around 250 addresses to one Wifi router. Yet, in real life, the speed rating of access points can give you an idea of how much devices one router can handle. For instance, a Wifi router of 400 Mbps with 100 devices connected will operate on average 4 Mbps for each.
Security of Wi-Fi has raised some concerns recently when WPA2 encryption was broken, that led to a major key replay attack, known as KRACK. In 2018, WPA3 was rolled out with the support for 128-bit (192-bit in WPA3-Enterprise mode) encryption.
But how to build a smart home app that would be well-tailored both for hubs and all devices?
Choose the scale...
Naturally, when developing a smart home app, one should decide how many products it is supposed to cover. One has two basic options.
- A single-purpose app. If you want to build an app to manage only one specific product - whether it’s a smart light bulb, kettle, thermostat etc. - this is what you need. Such apps are easy to develop, which means they can provide the top-notch user experience. However, consumers will require a bunch of apps to control a single smart home, the comfort of which is questionable.
- A multi-purpose app. If your aim is to embrace all smart home systems under one app, then a multi-purpose app is what you need.
According to the research, conducted by Alarm.com, namely this app type is most favored by the consumers.
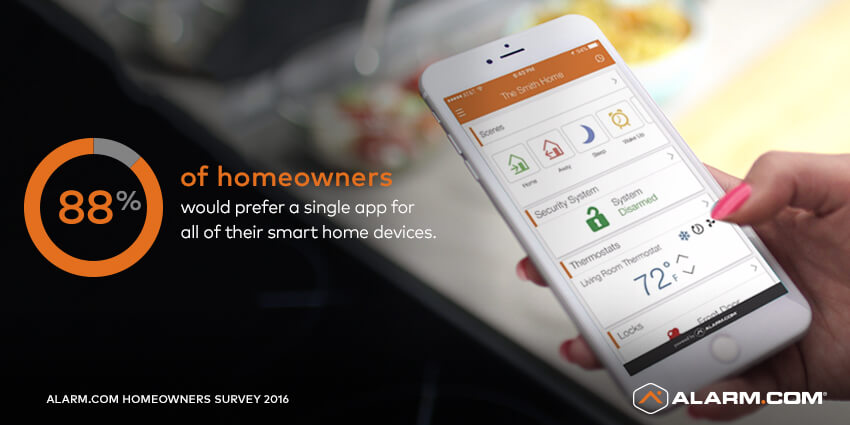
‘It takes a true smart home, not a collection of devices, to create the kind of experience homeowners expect. They want devices to work together to proactively make the home safer, smarter and more efficient, and a single app to control everything.’
Alarm.com
Yet, the approach needs more time, resources, and a team of highly-skilled professionals for its development.
Belitsoft is glad to provide a team of first-class IoT developers to build smart and highly secure smart home apps right for your business. Feel free to contact us to learn more!
...and method
Basically, one can go two ways: use a ready-made platform or develop everything from scratch by themselves.
- Using a ready-made platform:
When developing for a smart home, it is worth considering these 4 basic tiers of an IoT app:
- the device tier - the things themselves;
- the ingestion tier - software and infrastructure that gathers and arranges data from the devices. It also manages them and updates the firmware when necessary;
- the analytics tier - responsible for organizing and processing of data;
- the end-user tier - the application as your user sees it.
‘As a developer, you're unlikely to have the tools for dealing with the edge devices or gateways, or capabilities suitable for the ingestion tier anyway.’
Frank Gillet, a principal analyst at Forrester
It leaves developers working on the analytics and end-user tiers and for that, it makes sense to use already existing IoT platforms.
‘These platforms usually include an ingestion tier that carries out time-series archiving for incoming data, as well as an analytics tier, thin provisioning, activation and management capabilities, a real-time message bus, and an API to allow communication between the platform and applications built on top of it.’
Paul Rubens, a tech journalist for BBC, CIO.com and others
The most popular ready-made smart home platforms today include Microsoft Azure IoT Suite, Amazon Web Services, IBM Watson, Oracle IoT, KAA IoT, Google Cloud IoT. Some lesser-known vendors are Xively (now a part of Google), Mnubo, Bug Labs, ThingWorx and the like.
Moreover, simplified development enables to provide a better user experience. This, in its turn, encourages people to spend more on smart home solutions.
Another advantage of a ready-made platform is its proven scalability. The Internet of Things is a nascent, but promising market, application providers should be ready to scale their offerings.
- Writing a custom system:
Writing a smart home app from the ground up is challenging and long.
‘That would have been a considerable amount of work. Building our own back end would have slowed us by about one or two years. We would be significantly behind if we had done that.’
Lance Donny, OnFarm CEO
Custom smart home app development may be more sticky, but it allows to create a personalized and original solution.
Is smart home secure?
The smart home is a far less secure place than you possibly think. The IoT vulnerability is multi-faceted and results form the flaws at all levels.
Recently, a team of Ben-Gurion University conducted research, where they tested 16 devices (baby monitors, doorbells, cameras, temperature sensors, [etc.]) and found menacing flaws in 14 of them.
This makes the IoT devices an easy tool to launch cyber attacks.
‘Imagine that you get access to thousands or even millions of these devices and then you orchestrate them towards a given server and then you have a big attack. This was like the recent Mirai attacks – and you can run ransomware on top to get people to pay you to unlock their devices.’
Vangelis Ouzounis, Head of Secure Infrastructure & Services Unit within ENISA’s Core Operation Department
This is what happened in October 2016, when multiple distributed DDoS attacks rendered big names, including GitHub, Twitter, Reddit, Netflix, Airbnb unavailable. The strikes were supposedly performed through a botnet of multiple IoT devices, such as printers, IP cameras, residential gateways and baby monitors infected with the Mirai malware.
‘No one is going to keep the door to their house unlocked. You need to think [the same way] about the appliances on your network.’
JD Sherry, vice president of technology and solutions at Tokyo-based antivirus-software maker Trend Micro
Smart devices are not just prone to hacker attacks. They also put at risk the devices connected to your WiFi as they are an entry point into your network.
‘Part of the vulnerability is due to the ease with which consumer goods can be cracked. If the default passwords are not changed bypassing them is relatively simple. A patch can be introduced retroactively, but until then, the device could be a single entry point into an entire private network, enabling hackers to uncover sensitive data or relay false information.’
Tom Lysemose Hansen, founder, and CTO of Norwegian app security firm Promon
‘Your data is sent directly to the cloud, or first via ZigBee, Z-Wave or similar, to a smart-home hub, and then to the cloud. You then access this data and send commands to your devices with a mobile application, and you use, e.g., your Facebook account to register the application to the cloud service.’
Mika Ståhlberg, CTO at Finnish antivirus firm F-Secure
‘It's possible that a hacker could steal a password to retrieve personal data or manipulate a device. He could also hack the cloud backend of that service, or gain access to device data through physical access.’
Mika Ståhlberg
The vulnerability issue is also largely a result of the lack of security standards for the sector as a whole. Governance and deployment of patches and updates to hardware and software are carried out disjointedly.
This is backed up by the 2017 Study on Mobile IoT Application Security study conducted by Ponemon Institute. The researchers found out the reasons why mobile and IoT apps may contain vulnerable code.
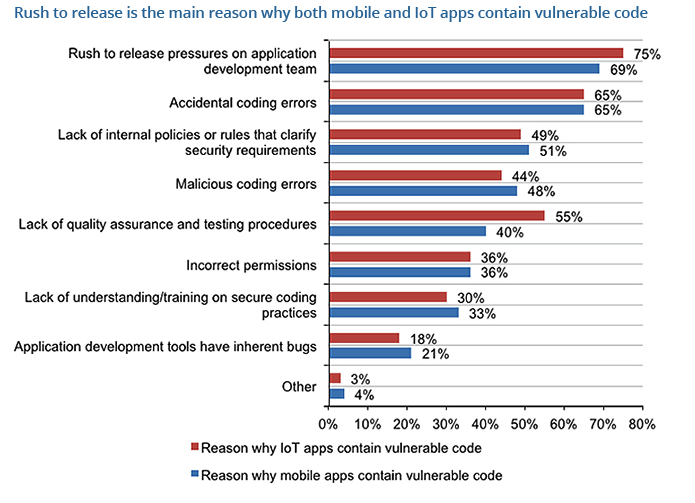
One of the solutions is to use established IoT application software development platforms. As a rule, they offer many secure IoT app elements like authentication that protects from brute force attacks.
‘The security of the IoT hinges on the apps used to access, monitor and control the device – whether it’s a mobile app used to control a doorbell or a teddy bear. It is crucial this app is able to self-protect, otherwise sensitive data, such as passwords, may be leaked and misused. Ideally, the device should verify that it’s being accessed from a trusted app, and this verification process should not rely on single static factors, like default passwords, but multiple factor authentication to ensure the integrity of the private network.’
Tom Lysemose Hansen
The vendors of well-engineered platforms are constantly polishing the software out, that allows you to avoid introducing inherently vulnerable code.
‘As a general security statement, we get most benefit when developers aren't doing anything. If car drivers were responsible for implementing their own airbags, they probably wouldn't work. Secure frameworks are key, and they should provide simple hooks for developers.’
Daniel Miessler, an information security professional
‘Robust frameworks can certainly help - but you do need developers who know how to use them properly and implement security properly.’
Diana Kelley, currently Cybersecurity Field CTO for Microsoft
IoT apps interact directly with internet-connected devices, which may have insecurities in their firmware. It is, therefore, vital to provide IoT apps with the mechanisms for secure firmware updates.
OWASP, the application security community, released a guide for secure coding practices. Some of the tips given include ensuring that devices are able to process encrypted update files and that cryptographic signatures are used and verified before installation.
And as it is difficult to secure IoT devices physically, all the data they keep should be properly encrypted. This makes the data useless for the perpetrator without the matching decryption key or password. Encryption will not solve the access control problem, but it will limit data loss even if access controls are bypassed.
Features of Smart Home App
According to Alarm.com’s “What Do Homeowners Really Want From the Smart Home?” survey, 54% of customers think that smart home products are too complicated to understand and set up. This amounts to roughly half of the consumers potentially avoiding using a product.
Since a smart product configuration usually involves a relevant mobile app, this is where the trouble comes. Often they are too complicated to understand and overloaded with unneeded functions. That is why for users to love your app, it should be as simple as possible. It matters.
However, simple does not mean defective. Despite the variety of devices and their features, there is always a set of standard functionality that every decent smart home monitoring app should include:
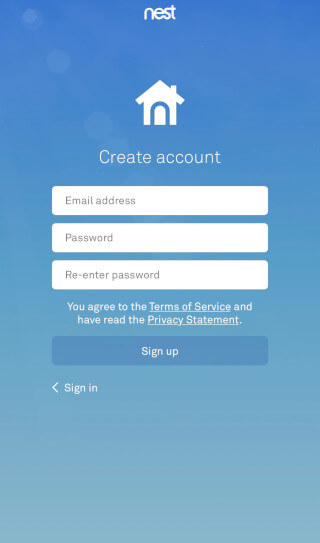
- Registration screen. Any smart home app is all about data security. It is better to explicitly ask your users for a name, phone number and e-mail address and send a verification code instead of simply allowing them to register with a network profile, for example.
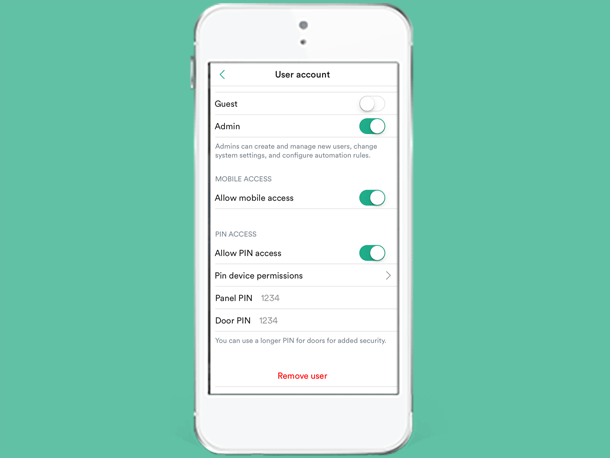
- Access configuration.After the user is in, it is necessary to offer two types of configuration profiles:
- admin with a complete set of managing rights
- a user with restricted access to the functions granted by an admin.
 Source: vivint.com
Source: vivint.com
3. Onboarding guide. Your users will appreciate if you dedicate some pages to explain the basic principles of how the smart home solution works and how to connect with the hub and smart devices.
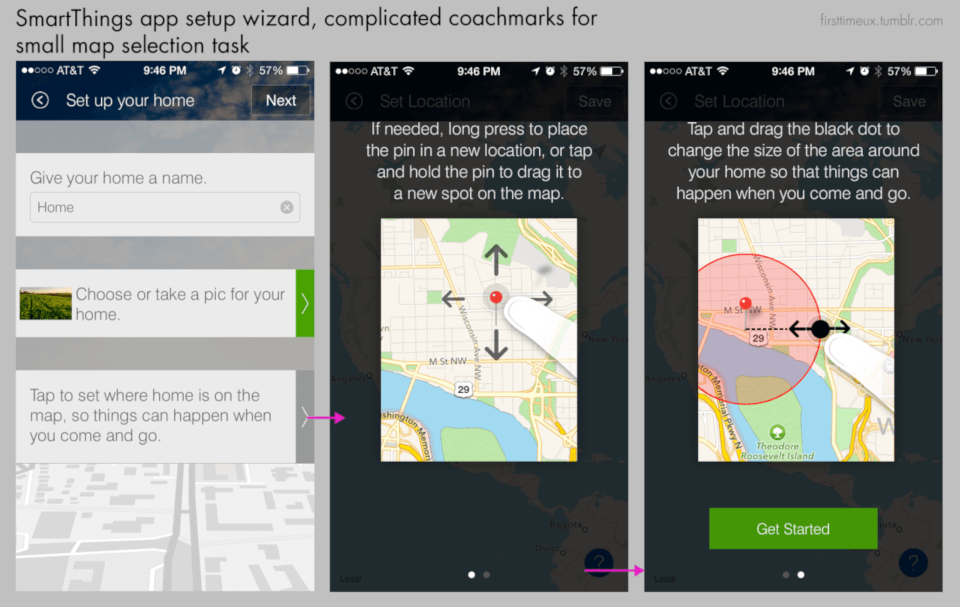 Source: firsttimeux.tumblr.com
Source: firsttimeux.tumblr.com
4. Devices and sensors screens. The page with a list of devices active in your smart home: camera, thermostat, locks, water sensors, light bulbs and so on. There should also be a separate management page for each.
 Source: nestcamlogin.com
Source: nestcamlogin.com
5. Groups and scenes.
The features allow users to organize their devices in specific groups. The support of scenes enables to set predefined configurations to a group of devices and launch them with a single tap or voice command.
‘For example, a customer could say, “Alexa, turn on bedtime” resulting with specific lights turning off, a bedroom light changing color to a low-lit orange-hue, a ceiling fan turned on, and the temperature changed to an ideal setting for sleep.’
Michael Palermo (Amazon)
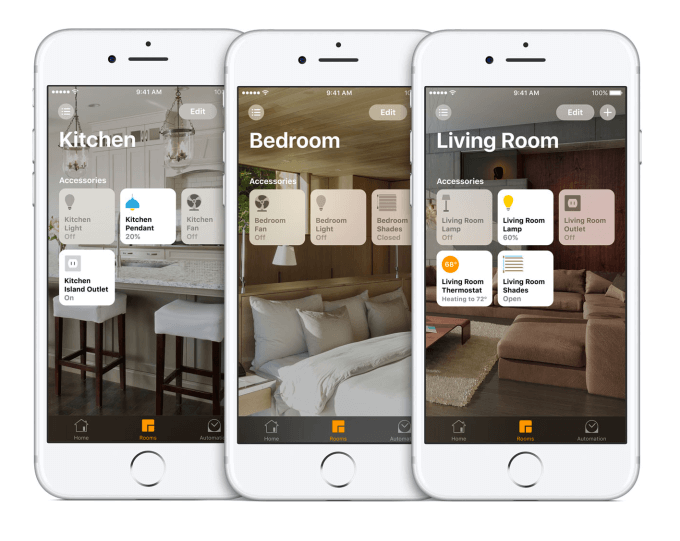 Source: techcrunch.com
Source: techcrunch.com
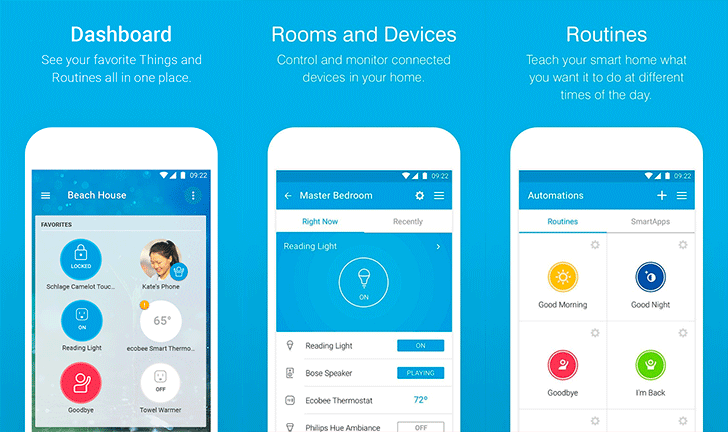 Source: https://www.androidpolice.com
Source: https://www.androidpolice.com
6. Push notifications. An app should always alert its users to all the actions within the smart home system, whether it is water leakage, fire alarm, trespassing, etc. or other users switching off the lights. It is reasonable to enable a special notification signal and make it loud even when the phone is in a silent mode.
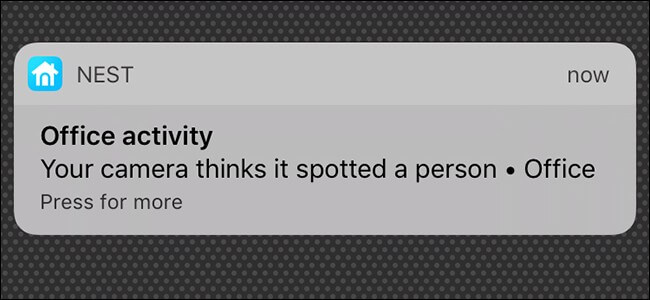 Source:howtogeek.com
Source:howtogeek.com
Some good examples
Vivint Smart Home
Vivint app helps users to control their cameras, thermostats, door and window sensors, smoke detectors etc. One can see and speak with front-door guests from anywhere with Vivint Doorbell Camera or get push notifications if the doors are open. One can download it either for iOS or Android device.
Alarm.com
The application is designed to allow to monitor an Alarm.com-enabled security system from anywhere. You can promptly get notifications about everything that is happening in your home and watch the video from the camera either live or recorded. It can also control your lights, temperature, door locks and much more. iOS and Android versions are supported.
June
June is aimed at controlling a June Oven and allows to manage the cooking process from anywhere. With June you can remotely preheat your oven, regulate the temperature and time and watch the whole cooking process on your smartphone. Currently, the app is available only for the App Store.
Kasa
Kasa allows users to manage connected TP-LINK Smart Home devices from anywhere in the world. You can set your devices in on or off mode according to your schedule and switch to away mode. The app also makes it possible to connect to Amazon Echo, Dot, Tap and The Google Assistant for voice control. It is available both for Android and iOS. Currently, it is compatible with a rather limited range of products.
FTTT
IFTTT enables users to create conditions between apps and other devices. Users can make the app perform certain actions under predefined circumstances. For example, you can set your smart light bulbs automatically turn on when you check your phone after the night sleep. IFTTT also supports voice control with Amazon Alexa and Google Assistant. You can download it both on your iOS and Android device.
Final thoughts
The smart home is a complex and interconnected system, and therefore requires a holistic approach to its development. The success of an app largely depends on the skills of its developers.
Belitsoft has a tech team of full-stack IoT application developers and experts. We are dedicated to delivering robust and scalable products to connect your smart home to your mobile. Contact us for a free quote!
Recommended posts
Our Clients' Feedback


















.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
![How to Create a Language Learning App [The Ultimate Guide!]](/uploads/images/blog/posts/previews/image_155352483594-image(600x250-crop).png)
.jpg)
.jpg)
.png)
.png)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.png)
.jpg)
.jpg)
.jpg)
.jpg)
.png)
















We have been working for over 10 years and they have become our long-term technology partner. Any software development, programming, or design needs we have had, Belitsoft company has always been able to handle this for us.
Founder from ZensAI (Microsoft)/ formerly Elearningforce